Something shifted at RSAC 2026 last week. The conversations that previously orbited around "how do…
0 Comments

The Agentic AI Security Crisis Is Here, and OpenClaw Proved It.
OpenClaw became the most-starred repository in GitHub history in about 60 days. By early March,…
0 Comments
Post-Quantum Cryptography: What Enterprise Security Teams Need to Know
I keep hearing about post-quantum cryptography. It comes up in industry reports, vendor announcements, and…
0 Comments

AI Just Did What Hiring Never Could for Cybersecurity
We've been talking about the cybersecurity workforce shortage for over a decade now. At this…
0 Comments

Before We Secure AI, We Need to Agree on What We’re Talking About
It's been a minute since I posted here. I've been heads-down in the security trenches,…
2 Comments

Private AI Security: Protecting Enterprise AI Systems and Sensitive Data
Key TakeawaysCombining data privacy protection with AI system safeguards enterprise AI implementations from unauthorized access…
0 Comments

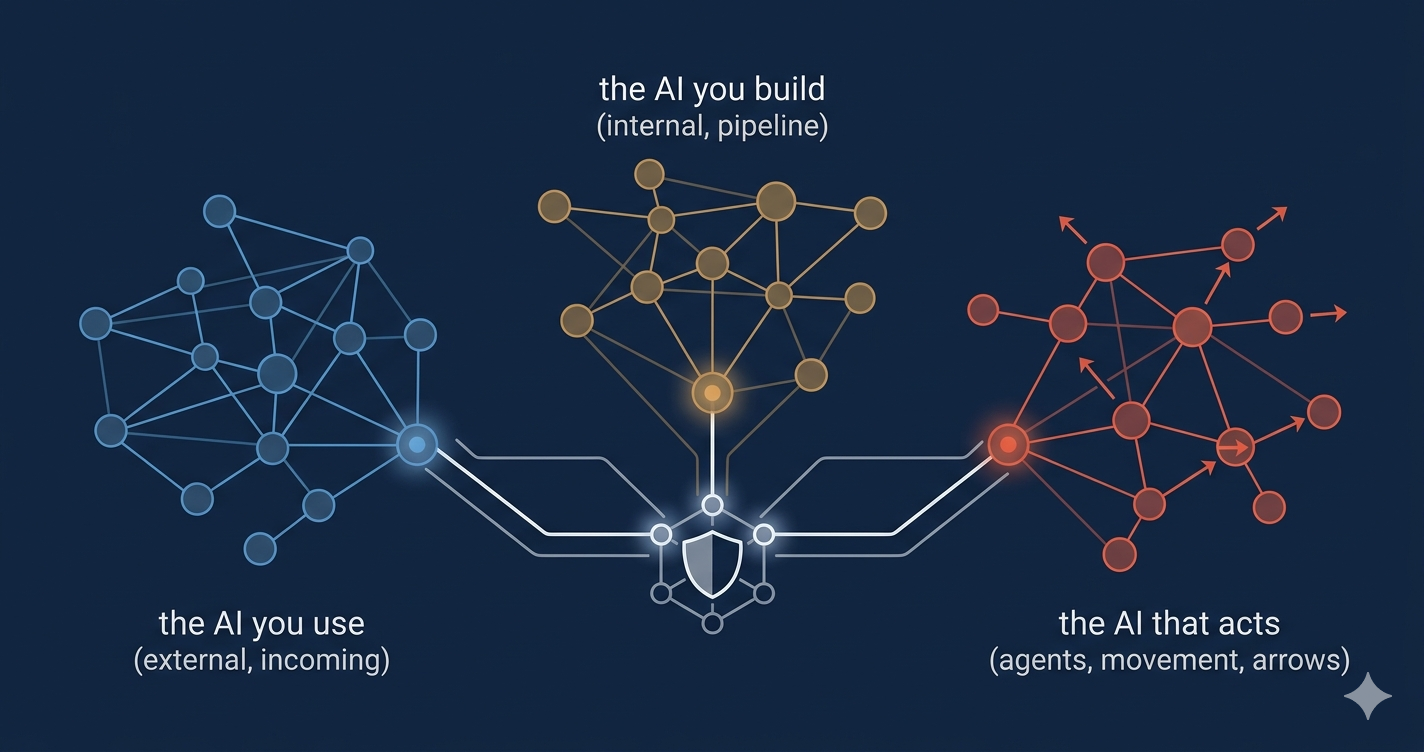
Zero Trust AI Security: Securing the AI You Use and the AI You Build
Key TakeawaysZero trust AI security requires distinct approaches for AI systems that enterprises consume versus…
0 Comments

AI Security Zero Trust: Comprehensive Protection for Modern AI Architectures
Key TakeawaysZero trust security model provides essential protection against unique AI threats, including adversarial attacks,…
0 Comments

Zero Trust has failed
I was recently made aware of this article coming out of DEF CON. I havent…
0 Comments

AI and Cybersecurity: Top Benefits, Risks, and Defense Strategies
AI is transforming the field of cybersecurity by improving how threats are detected and managed.…
0 Comments

Securing the Future: Best Practices for Generative AI Enterprise Security
Generative AI can transform enterprises, but it comes with significant security risks. This article dives…
0 Comments

VPN Is Dead: Exploring Modern Solutions for Secure Remote Access
Is the VPN dead? Traditional VPNs are increasingly seen as insufficient for today’s security needs.…
0 Comments

SASE vs Zero Trust: Best Practices for Secure Access
Searching ‘SASE vs Zero Trust’? You likely want to know the key differences and which…
0 Comments

Understanding Secure Service: How to Protect Your Data in the Cloud
Want to keep your cloud data safe? Secure service solutions protect your sensitive information from…
0 Comments

The Benefits of Global Connectivity in Today’s World
The Benefits of Global Connectivity in Today’s WorldGlobal connectivity links the world through the Internet,…
0 Comments

Top Strategies for Implementing Zero Trust Security Today
Zero Trust Security is a cybersecurity concept that means not trusting any entity by default,…
0 Comments

What is Cyber and Security? Types, Importance, and How to Stay Safe
Cyber and security focuses on protecting digital devices and data from cyber threats. This article…
0 Comments

The Essential Guide to Managed Services Security: Protecting Your Business
Managed services security involves outsourcing your cybersecurity needs to specialized providers. This approach is crucial…
0 Comments

What is SASE? Understanding Secure Access Service Edge
We are operating in one of the most rapidly evolving and unpredictable digital environments in…
0 Comments

Zero Trust and SASE: Do They Serve Each Other?
The cybersecurity space is rife with buzzwords, yet two terms have dominated the conversation in…
4 Comments

SASE for Modern Enterprises: Overcoming Implementation Challenges
Secure Access Service Edge (SASE) is transforming enterprise security and networking. As remote work, cloud…
0 Comments
Zero Trust Security: Why It’s a Game-Changer for Cybersecurity
Honestly — conventional security models are no longer holding up. The era of the ‘castle-and-moat’ approach from…
0 Comments
AI in 2025: 5 Trends That Will Reshape the World
So we must understand one fancy term, "AI," which stands for artificial intelligence. If I say this is…
0 Comments

How AI is Transforming SASE Security: A Smarter, Proactive Defense
The Future of Cybersecurity: AI-Powered SASE Imagine a sprawling metropolis with security guards on every…
0 Comments

Harnessing the Power of Generative AI in Cybersecurity
With the rapid growth in the digital world, cybersecurity has become a notable concern for…
0 Comments