What is Cyber and Security? Types, Importance, and How to Stay Safe

Cyber and security focuses on protecting digital devices and data from cyber threats. This article explains its importance, especially for businesses and individuals, and offers strategies to stay secure online.
Key Takeaways
- Cyber security is essential for protecting data integrity, maintaining privacy, and preventing financial losses due to cyberattacks, which are projected to cost over $13 trillion by 2028.
- The three core principles of cyber security—Confidentiality, Integrity, and Availability—form the foundation for securing sensitive information against various cyber threats.
- Organizations must adopt a comprehensive cyber security strategy that includes advanced practices such as regular security awareness training, robust incident response plans, and effective identity and access management to safeguard critical systems from evolving threats.
Understanding Cyber and Security

Cyber security involves protecting computers and networks. It focuses on safeguarding data from unauthorized access and cyber threats. In our interconnected world, where digital devices and online services are ubiquitous, the relevance of cyber security has never been greater. This discipline involves safeguarding systems, digital devices, and data from cyber attacks to ensure privacy and data integrity.
The aim of cyber security is to protect sensitive information, maintain privacy, and ensure data integrity and availability. Effective measures prevent attacks, reduce data breaches, and minimize financial losses.
Exploring the importance of cyber security reveals the core principles that underpin it.
The Importance of Cyber Security
Projections indicate that by 2028, the global cost of cybercrime could soar to an astonishing $13.82 trillion, emphasizing the pressing necessity for substantial cyber security measures. It is imperative for companies to invest in strong cybersecurity defenses as a means to mitigate severe economic damages and sustain consumer confidence.
The healthcare sector has experienced a notable surge in cyber attacks with reports of 1,463 incidents occurring on a weekly basis in 2022 alone. These incursions pose threats beyond just exposing sensitive patient information. They disrupt vital health services which can endanger human lives. The shift toward telecommuting and increased online transactions have amplified system vulnerabilities and heightened the probability of such attacks.
Implementing rigorous cyber security practices is paramount to protect critical data from unauthorized access and ensure uninterrupted operational functionality across various sectors. Inadequate security measures place organizations at risk not only for significant financial detriment but also irreparable harm to their public image. The subsequent discussion will delve into key principles underlying successful strategies aimed at fortifying an organization’s defense against escalating cybersecurity challenges.
Core Principles of Cyber Security
At the core of cyber security lies a foundational trio known as the CIA triad, comprising Confidentiality, Integrity, and Availability. These fundamental principles are vital in protecting information and making certain that data is both secure and reliable.
The principle of confidentiality is pivotal for restricting access to sensitive information solely to those with authorized credentials. It serves as a guard against unwarranted intrusion and helps preserve individual privacy. To maintain confidentiality, strategies like encryption and stringent access controls are frequently implemented.
Integrity ensures that data modification requires proper authorization, preserving its authenticity and credibility. Conversely, availability guarantees timely access to information systems when they’re needed within agreed-upon service parameters. Collectively forming an indispensable framework for effective cyber security strategies are these interdependent tenets.
Types of Cyber Security Measures

Cyber security involves an array of strategies intended to shield organizations from a wide range of cyber threats. These strategies are essential in safeguarding confidential information and maintaining the reliability of computer systems. Organizations need to take a holistic approach, which includes fortifying software applications as well as deploying intrusion prevention systems for comprehensive cyber protection.
Key elements such as network security, endpoint security, and cloud security form the foundation of an effective cyber defense strategy. By focusing on these distinct yet interrelated areas of cyber security, various layers contribute collectively to protect vital systems against potential cyber attacks.
Network Security
The primary goal of network security is to block unauthorized access to computer networks while simultaneously granting secure entry points for those who are authorized. To protect computer systems, the implementation of hardware-based protective measures such as dongles, trusted platform modules (TPMs), and cases that are sensitive to intrusions is crucial. Two-factor authentication has become a standard practice in reducing the risks associated with user errors and breaches by unauthorized entities.
Technologies used in Intrusion Prevention Systems (IPS) proactively scrutinize network traffic with the intention of identifying and obstructing potential threats before they inflict damage. These systems play a pivotal role in detecting security incidents early on, helping ensure that computer networks remain protected against attacks from external sources.
To Bolster network security against direct-access assaults, techniques like disk encryption alongside Trusted Platform Modules have been adopted extensively. Collectively these strategies form an all-encompassing shield designed to combat an array of cyber threats effectively.
Endpoint Security
It is crucial to safeguard individual devices like computers, laptops, smartphones, and IoT gadgets against cyber threats. These devices could become gateways for cyber attacks without adequate protection. Endpoint security strategies encompass the use of antivirus programs, intrusion prevention systems, encryption on devices, and continual updates to software.
To effectively manage endpoint devices with uniformity in applying security measures, Unified Endpoint Management (UEM) solutions are increasingly being utilized. By securing these endpoints diligently, one can notably diminish the likelihood of experiencing security breaches and the consequent loss of data.
Cloud Security
Before: As more businesses move their data to the cloud, the importance of cloud security has grown exponentially. Cloud security encompasses securing various elements. These include data, applications, infrastructure, access controls, data protection, and compliance. Due to the absence of a traditional security perimeter, cloud security is an essential part of a modern cyber security strategy.
Cloud security encompasses securing various elements, including:
- Data
- Applications
- Infrastructure
- Access controls
- Data protection
- Compliance
Due to the absence of a traditional security perimeter, cloud security is an essential part of a modern cyber security strategy.
The shared responsibility model delineates that while the cloud provider secures the infrastructure, customers are accountable for protecting their data. This model emphasizes the need for strong authentication and updated security protocols to protect sensitive data in cloud environments.
Access controls are crucial for ensuring that only authorized users can access sensitive information in the cloud. Application security measures help prevent unauthorized access and use of applications and data, thus reinforcing compliance standards. Adopting robust cloud security practices helps protect cloud-based services and assets from cyber attacks.
Common Cyber Threats and Attacks

The digital realm is riddled with numerous threats and attacks that have the potential to undermine data security and interrupt services.
Frequent types of cyber attacks include:
- Infections by malware
- Ransomware assaults
- Phishing schemes
- Distributed Denial of Service (DDoS) onslaughts
Such incursions can lead to consequences like identity theft, financial deception, and harm to the reputation of both individuals and companies.
Significant dangers within this landscape include hackers backed by state entities as well as insider threats. Both are considerable hazards for systems’ integrity. Recognizing these perils is essential in crafting robust security strategies that safeguard sensitive information along with critical infrastructure against such risks.
Malware Attacks
Malicious software, commonly referred to as malware, encompasses various types of harmful programs that are designed to intrude upon, damage or disrupt computer systems. The range of such malicious programs includes viruses, Trojans, rootkits and spyware – each characterized by its unique mode of operation and the specific type of harm it can cause. An early example is the widespread chaos triggered by the Morris worm in 1988 when it propagated across networks via malicious code.
The Stuxnet worm attack on Iran’s nuclear centrifuges in 2010 stands out as a prime illustration of how malware has been weaponized for geopolitical leverage. With infostealer malware usage spiking up by 266% and more than half of IT professionals acknowledging it as an alarming threat today’s security landscape faces increased complexity due to advancements in AI-driven malware.
Actors behind these malignant attacks span from mischief-seeking individuals to cyber vandals, and activists engaged in digital protestations through destructive means. From criminal enterprises seeking illicit gains to state-affiliated entities aiming at strategic targets—all exploiting weaknesses within software alongside human mistakes so they may infiltrate systems without permission. This underscores the critical nature of deploying stringent security precautions against such insidious incursions.
Phishing Attacks
Phishing involves manipulating individuals into divulging sensitive information or downloading harmful software by pretending to be a trustworthy entity through fraudulent communications. These attacks are especially deceptive because they mimic legitimate sources, making them harder to recognize. Spear phishing is an even more personalized strategy of phishing that utilizes publicly available data to deceive particular people or groups.
Cybercriminals utilize various methods during these attacks, like altering domain names, exploiting similar-looking characters (homograph attacks), and embedding dangerous macros in documents – all designed to give their fake messages credibility. Advanced scams such as business email compromise (BEC) have evolved into highly convincing schemes that can easily go unnoticed.
To counteract the threat posed by phishing campaigns effectively, businesses need comprehensive cyber security measures capable of intercepting and neutralizing malevolent emails before they ever reach employees’ inboxes. Implementing consistent security awareness training ensures staff members are equipped with the knowledge required to spot and sidestep these types of cyber threats, thereby diminishing the success rate of potential attackers.
Ransomware Attacks
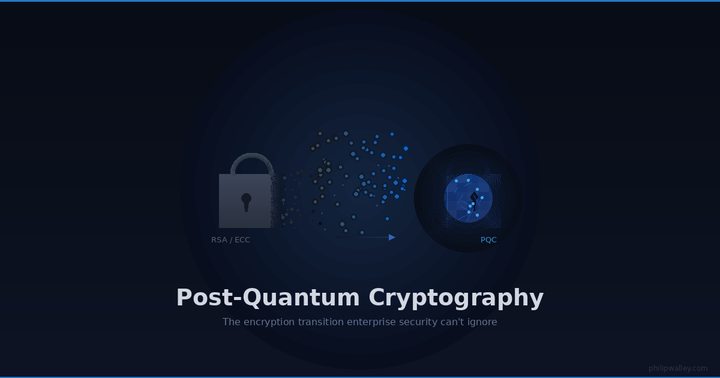
Ransomware is a form of malicious software that locks and encrypts the files of its victims, requiring payment for their release. These types of attacks utilize sophisticated methods such as asymmetric cryptography or combined encryption techniques to restrict access to data. In recent developments, attackers have adopted more coercive strategies like double extortion by exfiltrating sensitive information prior to locking it down, which intensifies pressure on victims to fulfill ransom demands.
Various sectors have been under siege by ransomware attacks, including public sector agencies, charitable organizations, and medical services providers. These incidents lead not only to operational disruptions but also to steep monetary damages. A prime example was the widespread WannaCry attack that starkly showcased how lucrative and far-reaching these cyber incursions can be.
To fend off threats from ransomware campaigns effectively, entities must commit resources toward comprehensive security measures encompassing consistent backups of critical data along with deploying advanced solutions designed for detecting emerging threats promptly. The advent of Ransomware as a Service (RaaS) platforms has simplified the process for criminals looking to perpetrate these schemes thereby escalating overall cybersecurity risks significantly.
Advanced Security Practices

It is crucial for both organizations and individuals to implement thorough cybersecurity strategies in order to protect themselves from the continuously evolving threats they face. These strategies should be multi-faceted, encompassing methods of threat prevention, detection, and reaction. Utilizing an array of tools and techniques that align with the specific security strategy of each organization is key to achieving robust cybersecurity.
In the realm of software development, prioritizing secure coding practices alongside formal verification processes is essential. The goal here is twofold: preventing inadvertent creation of security vulnerabilities and improving algorithm accuracy. When such advanced security measures are put into practice effectively, they greatly contribute to fortifying systems against potential breaches by bolstering their overall resilience.
Security Awareness Training
Educating users on the myriad of cyber threats through consistent security awareness training is key to fostering safe digital habits. Such training significantly reduces the risk of security breaches by boosting user knowledge about potential cyber risks and teaching them preventive measures.
Ongoing instruction in cyber security minimizes mistakes caused by human error while cultivating an environment where vigilance is second nature to users. As a result, individuals become more adept at recognizing threats and safeguarding against vulnerabilities, thanks to this improvement in understanding and self-protection strategies.
Threat Detection and Response
Utilizing analytics-oriented solutions is vital for the prompt detection and counteraction of cyber threats. Systems known as Security Information and Event Management (SIEM) are widely deployed to consolidate security-related data, generating notifications that aid security teams in addressing incidents with increased efficiency.
An overabundance of alerts can lead to alert fatigue among these teams, thereby complicating their ability to identify legitimate issues. Adopting strategies like threat intelligence and employing machine learning techniques such as User and Event Behavioral Analytics (UEBA) can assist in reducing this overload by focusing on genuine threats.
In order to thwart insider threats effectively, organizations should employ User and Entity Behavior Analytics (UEBA) alongside Privilege Access Management (PAM), while embracing zero-trust frameworks that ensure every access request is continuously verified.
Vulnerability Management
The process of vulnerability management encompasses the ongoing identification, remediation, or mitigation of security vulnerabilities within systems and applications. It is vital to continuously monitor and conduct periodic evaluations in order to detect and resolve security weaknesses before they are exploited.
Organizations must perform consistent risk assessments to grasp possible vulnerabilities that could affect their operations, which serves as a foundation for crafting incident response plans. The effectiveness of addressing newly identified vulnerabilities hinges on maintaining current vulnerability management tools through regular updates from vendors.
Conducting routine penetration testing aids organizations in uncovering any existing flaws in their systems. This ensures that implemented security measures are strong and capable of safeguarding against potential breaches.
Protecting Critical Systems

Ensuring the uninterrupted and dependable operation of critical systems is crucial for societal stability. This entails securing vital infrastructure operations such as those in healthcare and finance against cyber threats, to maintain the continuous delivery of important services.
The objective of disaster recovery plans is to swiftly reinstate critical systems while minimizing disturbance to business activities. To lessen the effects of data loss during a cyber event, it’s imperative to keep current backups as an essential component of these strategies.
Critical Infrastructure Security
The importance of cybersecurity is paramount to the protection of national security. Its fundamental responsibilities encompass thwarting cyber warfare and defending essential resources. Cyber attacks pose a significant threat to national safety as they often aim at crucial infrastructure, government operations, and military bases. By securing critical infrastructure, we maintain uninterrupted delivery of vital services, which are indispensable in averting threats to public welfare and overarching national security.
Essential systems such as energy networks, transport hubs, healthcare frameworks, and communication channels constitute critical infrastructure. The power industry is notably susceptible. Any disturbances can have extensive consequences on various sectors reliant on consistent electrical supply.
Agencies like the Cybersecurity and Infrastructure Security Agency (CISA) along with the National Institute of Standards and Technology (NIST) provide strategic counsel for safeguarding this crucial infrastructure. Specific cybersecurity standards for nuclear establishments are mandated by entities such as the U.S Nuclear Regulatory Commission.
IoT Security
Protecting internet-connected devices, or IoT devices, from cyber threats is a critical aspect of cyber security. IoT devices can serve as entry points for cyber attacks due to their interconnected nature and varied security standards. The risks associated with IoT devices include increased potential for cyber attacks and misuse, including cyber-kinetic attacks.
A zero trust approach is required to protect against supply chain attacks involving IoT devices. This approach continuously verifies and monitors access requests, ensuring that only authorized users can access sensitive data.
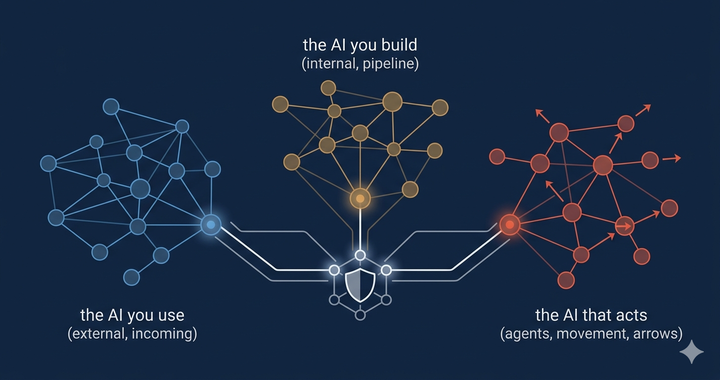
Emerging Trends in Cyber Security
As cyber threats continue to evolve, resource-strained security teams are turning to advanced analytics, AI, and automation to enhance cyber defenses. AI-driven cyber threats can breach security systems, highlighting the dual role of AI in cyber security. Proactive measures and strategic planning are becoming increasingly important in addressing cyber security challenges.
Phishing tactics have evolved to include sophisticated variations such as vishing and smishing, which exploit trust through phone calls and text messages.
Attack surface management (ASM) focuses on continuous discovery, analysis, and monitoring of cybersecurity vulnerabilities, helping organizations stay ahead of emerging threats.
AI and Machine Learning in Cyber Security
The implementation of AI and machine learning technologies has enhanced the ability to identify trends within data, significantly increasing both the pace and precision in recognizing potential threats. These advancements have led to automation in security-related decision-making processes, which not only improves response actions to threats, but also alleviates some of the workload carried by security teams.
AI solutions are proving indispensable for streamlining threat identification and accelerating reaction speeds. Imperva’s Attack Analytics is an example where these innovations leverage AI and machine learning capabilities to bolster security protocols while prioritizing critical security occurrences.
Zero Trust Architecture
The Zero Trust Architecture implements stringent access controls by confirming every request for connection, thereby guaranteeing that resources are accessible solely to users with proper authorization. Its increasing popularity stems from its insistence on continuous verification of all devices and individuals attempting to access those resources, based on the presumption that threats could emerge both within and beyond the confines of the organization.
Significantly impacting cyber security practices is Zero Trust Security due to its relentless scrutiny and authentication of access petitions. By doing so, it establishes a solid defense against cyber threats. Employing this strategy bolsters an organization’s defenses against potential dangers originating internally or externally, thus fortifying their overall stance on cybersecurity.
Regulatory Compliance
Companies are under considerable stress to adhere to regulatory standards, which has heightened the emphasis on strategies for protecting data. The GDPR stands out as a critical regulation that bestows on EU citizens rights concerning data protection, underscoring the necessity of adhering to these rules within the realm of cyber security.
Incident Response and Recovery
To mitigate harm and be ready for potential cyber threats, it is essential to have a robust incident response strategy. Formal incident response plans typically include the implementation of detection and response technologies as standard practice to boost security measures. To effectively manage and recover from cybersecurity incidents, organizations need both a carefully formulated strategy and the adoption of suitable technologies.
In the United States, managing the system for responding to these incidents, overseeing risk management programs, and setting requirements for cybersecurity fall under the jurisdiction of the National Cyber Security Division. They provide a structured framework designed to facilitate an effective response in case of such incidents.
Incident Response Planning
Computer security incident management aims to avert potential breaches or defend against cyberattacks. Standard response strategies for such incidents involve documented procedures that detail the actions required during an attack, incorporating comprehensive playbooks defining the tasks and duties of each member within the incident response team.
Acting swiftly when systems are compromised is crucial in reducing exploited weaknesses and curtailing any associated losses. The purpose of a computer security incident response plan is not only to manage and control incidents, but also to curtail their impact while aiding in subsequent restoration efforts.
Disaster Recovery
Having robust disaster recovery measures in place is crucial for preserving business continuity and effectively addressing threats amidst a cyber attack. By employing these disaster recovery strategies during such incidents, an organization can continue its operations without succumbing to ransom demands, guaranteeing that vital systems stay operational.
It’s imperative to regularly back up data and have proper insurance as key tactics to lessen the repercussions of potential data loss. When organizations keep their backups current, they are equipped to quickly recover any compromised data, thereby reducing the detrimental consequences of cyber attacks.
Cyber Security Tools and Solutions
Tools dedicated to cybersecurity are vital in identifying, thwarting, and managing cyber threats. They safeguard crucial infrastructure, ensure the security of data, and defend computer systems against diverse forms of cyber attacks. The Cybersecurity and Infrastructure Security Agency (CISA) offers a repository of complimentary cybersecurity services and tools that aim to bolster the security measures of organizations.
For instance, sophisticated cybersecurity instruments like Runtime Application Self-Protection (RASP) as well as Imperva API Security contribute greatly to the protection of applications and APIs from established threats as well as emergent zero-day exploits. By monitoring application code live-time, they can spot vulnerabilities immediately, thus mitigating potential exploitation without having to depend on predefined patterns associated with particular kinds of attacks.
Identity and Access Management (IAM)
IAM (Identity and Access Management) systems implement access controls that stipulate the conditions under which information and systems within an organization can be accessed. A crucial element of IAM frameworks is multifactor authentication, which bolsters security through the need for various verification methods.
The adoption of IAM solutions can greatly diminish the chances of unauthorized entries and data breaches. By managing user permissions to organizational assets and improving security measures overall, IAM holds a vital position in safeguarding organizational data.
Data Loss Prevention (DLP)
Tools for Data Loss Prevention (DLP) are pivotal elements in cybersecurity protocols, indispensable for the oversight and regulation of data transfers to protect confidential information. They aid in averting data breaches by ensuring that sensitive data is neither inadvertently disclosed nor falls into the hands of unapproved individuals.
In the realm of cloud security, where remote storage and access to data are common practices, DLP tools assume enhanced significance. Through these solutions’ deployment, companies can defend their information against unauthorized acquisition and maintain adherence to established regulations concerning data protection.
Intrusion Prevention Systems (IPS)
Intrusion Prevention Systems (IPS) are sophisticated technologies implemented within advanced network security measures to identify and counteract threats before they can inflict damage. These systems scrutinize network traffic for any signs of dubious activity and proactively intervene to thwart intrusions, thereby safeguarding crucial systems.
Utilizing IPS enables enterprises to bolster their defense against cyber attacks, significantly diminishing the likelihood of breaches. Such systems play a vital role in preserving the integrity and accessibility of computer networks, ensuring that sensitive information is kept secure.
Summary
In essence, cyber security stands as a vital component in our progressively technology-driven society. Recognizing the significance of shielding sensitive information and embracing sophisticated security tactics and instruments underscores that all-encompassing cyber security actions are indispensable for defense against digital dangers. The fundamental tenets of confidentiality, integrity, and availability lay the groundwork for effective cyber security approaches, guaranteeing data remains protected and reliable.
As digital threats become more complex with time, remaining vigilant and ahead of the curve is imperative. By adopting stringent security protocols, engaging in continuous training sessions, and deploying cutting-edge technologies. Both organizations and individuals can defend their informational assets and infrastructures from malicious cyber incursions. May this guidance motivate you to bolster your digital defenses proactively for a more secure online environment moving forward.
Frequently Asked Questions
What is the primary objective of cyber security?** **?
The fundamental goal of cyber security is to protect information against threats and illicit entry, ensuring the confidentiality, integrity, and accessibility of data. This protection of sensitive data is crucial for preserving confidence in electronic systems.
Why is security awareness training important?** **?
Security awareness training is essential as it educates users about cyber threats and promotes safe online practices, significantly reducing the risk of security breaches.
By enhancing awareness, organizations can foster a more secure digital environment.
What are some common types of cyber attacks?** **?
Common types of cyber attacks include malware infections, ransomware, phishing, and distributed denial-of-service (DDoS) attacks. These threats can lead to serious consequences such as identity theft, financial fraud, and damage to reputation.
How does a zero trust architecture enhance cyber security?** **?
A zero trust architecture significantly enhances cyber security by implementing rigorous access controls and continuously verifying all connection requests, which ensures that only authorized users can access sensitive resources.
This approach minimizes the risk of unauthorized access and potential breaches.
What role do Intrusion Prevention Systems (IPS) play in network security?** **?
In the realm of network security, Intrusion Prevention Systems (IPS) play a critical role by actively scrutinizing and assessing traffic to identify possible threats. Their capability to rapidly respond prevents breaches from causing harm before they can inflict any damage.
By employing this vigilant strategy, IPS markedly improves the robustness and protection of network ecosystems, ensuring their safety and integrity remain intact.

Comments ()