SASE vs Zero Trust: Best Practices for Secure Access

Searching ‘SASE vs Zero Trust’? You likely want to know the key differences and which is better for your organization. This article explains what SASE and Zero Trust are, their unique strengths, and how to choose between them.
Key Takeaways
SASE (Secure Access Service Edge) integrates various security tools into a unified cloud solution, enhancing efficiency and operational management in modern network security.
Zero Trust emphasizes strict access controls, necessitating continuous verification of user identities and minimizing trust within the network to safeguard against unauthorized access.
Combining SASE and Zero Trust creates a robust security framework that enhances visibility, simplifies management, and improves compliance with regulatory standards for organizations.
SD-WAN
FWaaS (Firewall as a Service)
WAAP (Web Application and API Protection)
CASB (Cloud Access Security Broker)
SWG (Secure Web Gateway)
DLP (Data Loss Prevention)
Persistent verification and access controls to support compliance with different regulatory mandates
Monitoring of threats as they occur
Automated reactions to possible security breaches
Implement Zero Trust Network Access (ZTNA): Adopting a Zero Trust Network Access (ZTNA) solution is fundamental in providing secure access to applications and services. ZTNA operates on the principle of “never trust, always verify,” ensuring that only authenticated and authorized users can access network resources.
Use Multi-Factor Authentication (MFA): Multi-factor authentication adds an extra layer of security by requiring users to provide multiple forms of verification. This significantly reduces the risk of unauthorized access, as it ensures that users are who they claim to be.
Verify Device Health: Ensuring that devices meet specific security standards before granting access is essential in reducing the attack surface. Regularly verifying device health helps in identifying and mitigating potential vulnerabilities.
Restrict Access Based on User Identity and Device Health: Implementing access controls that consider both user identity and device health is crucial in minimizing security risks. By restricting access based on these factors, organizations can ensure that only trusted users and devices can interact with sensitive resources.
Implement Secure Access Service Edge (SASE): Deploying a SASE solution provides secure, optimized access to network resources from any network. SASE combines secure access, network security, and access service edge capabilities, creating a robust security framework.
Simplify Security Policy Management: Streamlining the management of security policies is vital in maintaining an effective security posture. SASE simplifies this process by centralizing control, making it easier to enforce consistent security measures across the entire network.
Ensure Secure, Optimized Access: Providing secure, optimized access to network resources from any network is essential in supporting remote work and cloud services. SASE ensures that users can securely connect to the network, regardless of their location.
Understanding SASE and Zero Trust
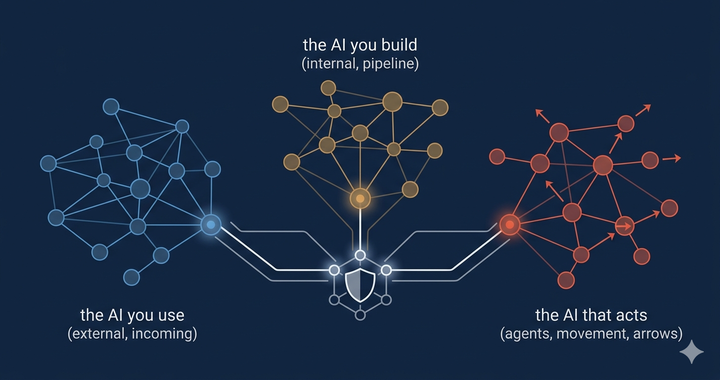
SASE and Zero Trust represent innovative strategies for bolstering security within cloud-focused environments of today. These methodologies mark a departure from conventional, perimeter-centric security measures to an emphasis on controlling access, thereby revolutionizing the framework and execution of network security. SASE’s main objective is to protect networks while streamlining structures and elevating efficiency through a comprehensive approach toward safeguarding the network.
Conversely, Zero Trust zeroes in on rigorous identity checks alongside ongoing authentication to guarantee that only verified users and gadgets have access to specific resources. Both SASE and Zero Trust are built upon cloud-oriented deployment models, which render them flexible and expandable solutions suitable for contemporary business infrastructure.
As part of the integrated architecture provided by SASE, Zero Trust Network Access (ZTNA) plays an instrumental role in reinforcing defense mechanisms with tight-fisted access controls reliant on user credentials as well as established trust levels. Together these paradigms form a formidable barrier against digital threats, adapting easily to shifting boundaries while ensuring secure connections to applications housed in the cloud.
What is SASE?
Secure Access Service Edge, abbreviated as SASE, refers to a collection of security mechanisms designed for cloud-centric protection. This approach moves defense measures closer to the point of use and associated applications while also encompassing the Security Service Edge.
SASE amalgamates an array of distinct security instruments into one cohesive cloud-based service package.
By offering this integrated set of solutions, it forms a robust security framework for businesses by centralizing network control—this aids in applying uniform policies across the whole network infrastructure, which greatly bolsters operational effectiveness.
The architecture that SASE introduces is beneficial for remote work settings and hybrid workforce models. It circumvents traditional traffic rerouting through conventional data centers via its reliance on cloud gateways along with providing access services rooted in the cloud itself.
A primary benefit conferred by SAE lies within its capacity to reposition core security operations proximal to user locations at “the edge,” leading to amplified efficacy regarding safety postures. As organizations migrate their processes into the virtualized realm of clouds, integrating assorted functionalities under one all-encompassing secure networking umbrella enhances both adaptability and cybersecurity defenses.
SASE stands out due to its inclusive strategy that merges both networking elements with protective features, thus marking an evolution from isolated strategies such as standalone SASE or ZTNA offerings. Integrating SASE and ZTNA can further enhance security and efficiency in modern network configurations by combining broad network security strategies with secure application access through identity verification.
What is Zero Trust?
The Zero Trust security framework is predicated on rigorous access control, operating under the assumption that potential threats may be present both within and outside of a network’s borders. At the heart of this model lies the maxim “never trust, always verify,” mandating that all users and devices undergo authentication, authorization, and ongoing validation before receiving permission to access any resources. By adhering to a least privilege strategy, the zero trust approach guarantees individuals and devices are granted only those accesses essential for their specific functions.
Under this strict security regime known as Zero Trust Network Access (ZTNA), no user is inherently trusted. Instead, each request for network access must withstand rigorous scrutiny consistent with established security policies. This system advocates employing multi-factor authentication (MFA) alongside repeated reassessment of permissions in adherence to least privilege principles.
With remote work becoming increasingly prevalent, there has been an uptick in reliance on ZTNA frameworks which stipulate unequivocal verification prior to allowing entry into applications or services—thereby providing solidified defense mechanisms adaptable to shifting conditions.
Key Differences Between SASE and Zero Trust

SASE and Zero Trust both aim to fortify security but exhibit notable distinctions in range and execution. Zero. Zero. Trust centers on controlling access, with a stringent protocol that ensures only verified and approved users can reach certain assets.
In contrast, SASE represents an expanded spectrum of network and security services by fusing diverse technologies to bolster the overall defense mechanisms. Its inclusive design merges networking and security functions into one cohesive system that surpasses what Zero Trust offers on its own.
The core principles of zero trust serve as the bedrock for SASE infrastructure, guaranteeing secure access while amalgamating numerous security services. This synergistic approach enables entities to harness the benefits intrinsic to each framework—sase layered with zero trust—for a fortified and adaptable protection strategy.
By discerning the distinct features between SASE’s comprehensive coverage versus Zero Trust’s focused authorization controls, organizations are empowered to judiciously adopt these frameworks in alignment with their bespoke safeguarding requisites.
Scope and Application
SASE is engineered to deliver a variety of security and network features suitable for various corporate settings. It achieves extensive protection by implementing security across every application and data pathway, integrating elements like Next-Generation Firewalls (NGFW) and Secure Web Gateways (SWG). This expansive approach grants SASE the ability to maintain oversight over the entire network, guaranteeing consistent implementation and enforcement of security policies.
Zero Trust, on the other hand, concentrates on granting secure access specifically for remote users trying to enter certain applications or services. It underscores meticulous access control based on validating user roles. Zero Trust’s main concern isn’t networking capabilities. Rather, its core purpose lies in assuring that only authorized individuals gain entry to confidential resources.
Jointly, SASE and Zero Trust present an all-encompassing security framework that caters to distinct dimensions of network accessibility and reliability. These two solutions operate in tandem as complementary strategies serving contemporary enterprise needs.
Network Design Philosophy
SASE employs a cloud-centric design that combines security measures with SD-WAN, simplifying network administration while boosting protection. Thanks to its cloud-based nature, SASE can be implemented on an as-needed basis, cutting down on the intricacies and modifications to networks required by shifts toward cloud usage. By fusing networking and security functions into one unified offering, SASE seeks to lessen overall complexity and bolster operational effectiveness.
In contrast, Zero Trust implements stringent access controls without necessitating fundamental changes to existing networks. It concentrates on reducing redundant hardware clutter and tackling complicated network issues by imposing tight access restrictions based on user identities and device credentials.
By integrating SASE with Zero Trust principles, it’s possible to refine the IT environment to ensure sustained security but diminish the convolutedness often seen with conventional network designs.
Security Capabilities
SASE amalgamates an extensive array of security capabilities, encompassing Secure Web Gateways (SWG), Cloud Access Security Brokers (CASB), and Firewall as a Service (FWaaS). This creates an advanced security framework that extends beyond mere access control. The convergence of diverse security measures boosts overall network protection by enforcing granular access controls and impeding attackers’ ability to move laterally within the system.
As a vital element of Zero Trust architecture, Zero Trust Network Access (ZTNA) concentrates on authenticating identities and crafting secure pathways for both users and devices. ZTNA confines visibility and accessibility strictly to validated individuals, thereby blocking unauthorized entities from exploiting potential weak spots in the network.
Though SASE presents a wider spectrum of protective functions, the focus on identity authentication and continuous scrutiny central to Zero Trust is pivotal for devising a thoroughgoing security strategy.
How SASE Enhances Zero Trust Security

Merging SASE with Zero Trust significantly improves security measures by reinforcing identity checks and guaranteeing that only individuals with authorization can access network resources. Tailored to safeguard remote endpoints, IoT devices, and cloud-stored data, SASE is well-suited for the demands of a Zero Trust approach. Nevertheless, only deploying SASE isn’t enough to establish a comprehensive Zero Trust model. It requires more elements to ZTNA.
By integrating various security features within its framework, SASE offers increased oversight and thorough control over network safety. When combined with the rigorous access controls characteristic of Zero Trust principles, organizations are able to fortify their defense strategy while maintaining flexibility. This fusion advocates for persistent validation and scrutiny over user activity and connected hardware, which upholds the prevention of unapproved entry into the network’s confines.
Integration of Services
The SASE architecture elevates both security and performance for cloud-based applications through a unified solution that merges multiple security services. This encompasses:
Incorporating the elements of SASE alongside Zero Trust frameworks enables organizations to uphold compliance while safeguarding their IT landscapes.
Merging SASE with Zero Trust enhances an organization’s ability to fulfill various regulatory obligations by augmenting oversight and command over user access. This integrated strategy guarantees that entities can efficiently administer their security stance in alignment with industry norms and legal requirements.
Improved Management and Visibility
By merging network and security operations, SASE facilitates streamlined management within a single platform. This integration leads to greater operational efficiency by making it easier to handle multiple functions and services while decreasing the need for extensive resource commitments. The design of SASE grants instantaneous insight into network traffic, which enables the enforcement of proactive security strategies and swift reactions to potential risks.
Combining SASE with Zero Trust amplifies IT landscape oversight and closes security coverage loopholes. Enhanced control and increased transparency result in a more effective distribution of resources, thereby empowering security teams to concentrate on essential activities that guarantee ongoing protection against progressive threats to the network.
Access Control and Network Security with SASE
Secure Access Service Edge (SASE) represents a transformative approach in the realm of network security by converging network and security services into a unified, cloud-native framework. This innovative architecture ensures secure, optimized access to network resources from any location, effectively addressing the dynamic needs of modern enterprises.
SASE combines key capabilities such as secure access, network security, and access service edge, creating a comprehensive solution that simplifies the management of security policies. By integrating these elements, SASE provides robust protection for the entire internal network, extending secure access to both cloud networks and private network resources.
One of the standout features of SASE is its ability to streamline the enforcement of security policies across the entire network infrastructure. This enhances operational efficiency and ensures consistent application of security measures, thereby fortifying the network against potential threats. As organizations continue to embrace cloud services and remote work models, SASE emerges as a critical component in maintaining a resilient and secure network environment.
Benefits of Combining SASE and Zero Trust

Integrating SASE with Zero Trust significantly bolsters an organization’s security defenses. It results in stronger protection, more efficient processes, and heightened adherence to regulatory standards. The synergy of these two frameworks equips organizations with a robust and flexible network infrastructure that can respond effectively to the constantly evolving landscape of cyber threats.
When organizations deploy SASE in conjunction with Zero Trust principles across their dispersed branches, they are able to unify communication under consistent security policies and access controls. This holistic strategy does not just streamline the management of security measures. It also substantially reinforces the safeguarding of critical assets and sensitive information.
Enhanced Security Posture
Merging SASE with the Zero Trust framework results in a unified system that greatly improves both threat mitigation and user authentication processes. This holistic strategy perpetually verifies user permissions, blocking unapproved users from exploiting network weaknesses. The structure provided by SASE bolsters identity management and thwarts potential illicit access attempts, forging a stronger security model.
The confluence of SASE and Zero Trust enables organizations to not just meet but surpass established regulatory compliance criteria. Such an advanced security stance allows businesses to safeguard their sensitive information and vital resources effectively against emerging cyber threats while preserving the integrity and secrecy of their networks.
Simplified Security Strategy
Merging SASE with Zero Trust can lessen the complexity of security tools by centralizing control and making workflows more efficient. By providing a cohesive platform that eases the oversight of diverse network boundaries, SASE weaves together protective features such as data encryption and firewalls, aiding enterprises in adhering to regulations regarding data safety. This confluence fosters enhanced operational productivity while diminishing the need for extensive resource commitments, thus simplifying the workload for security teams in implementing and overseeing security policies.
Fusing security services within both SASE and Zero Trust paradigms streamlines an organization’s overall approach to safeguarding its systems, permitting focus on pivotal protection duties without getting weighed down by intricate management tasks across numerous instruments and applications. Such an integrated method amplifies effectiveness within cyber defense operations while guaranteeing uniform enforcement of security directives throughout every segment of the network infrastructure.
Cost Efficiency
By merging SASE with Zero Trust, organizations can achieve notable reductions in costs by cutting down on the necessity for distinct security solutions. Opting for unified solutions that amalgamate various security functions into one platform allows companies to slash the financial burden of administering and upkeeping multiple security tools. The economic efficiency gained from this integration is an essential factor for businesses when considering their network security tactics.
Embracing both SASE and Zero Trust models enables enterprises to maximize their security spending while securing a robust defensive stance. This collaborative strategy not only diminishes expenditures but also bolsters the overall efficacy of security measures, guaranteeing that resources are deployed in a manner that is both economical and effective.
Use Cases for SASE and Zero Trust

Frameworks like SASE and Zero Trust are crucial for contemporary businesses due to their extensive practical applications. They allow companies to safeguard their remote workers, secure cloud-based assets, and improve adherence to regulatory requirements. By adopting SASE and Zero Trust, organizations can guarantee safe entry points and shield confidential information from unsanctioned access or security incidents.
The utility of SASE and Zero Trust is evidenced by their ability to tackle multiple security concerns effectively. These frameworks serve as robust security measures capable of being customized for any organization’s unique demands—be it ensuring the protection of remote users’ connections, defending cloud infrastructures, or fulfilling mandated compliance obligations.
Securing Remote Workforces with Zero Trust Network Access
SASE and Zero Trust frameworks fortify secure connections for geographically dispersed individuals by confirming their identities and permissions via principles rooted in zero trust. The adoption of these structures allows companies to foster a more protected remote access setting, thwarting unsanctioned entry and boosting general security across networks. Compared to traditional VPNs, Zero Trust offers superior control over who is allowed access, making certain that only verified users have the capability to reach sensitive network resources.
These frameworks are indispensable for teams across various locations to secure remote connectivity. They provide a resilient security model that safeguards network assets' integrity and secrecy. Embracing SASE along with Zero Trust is fundamental for efficiently managing and protecting workforces operating remotely, thus preserving a vigorous defense posture amidst an evolving landscape where remote work is becoming increasingly common.
Protecting Cloud Resources
The SASE and Zero Trust models offer strategies for applying security policies within cloud frameworks, intending to safeguard sensitive information from unauthorized access and potential breaches. By combining various security services like CASB (Cloud Access Security Broker) and SWG (Secure Web Gateway), SASE bolsters data protection in the cloud while promoting adherence to industry regulations. Such a thorough stance on cloud safety permits organizations to competently oversee their cloud-based assets.
Implementing both SASE and Zero Trust principles fortifies the handling of sensitive content within cloud infrastructures, thus bolstering its defense against possible risks. This cohesive method towards securing clouds delivers a resilient structure that assures not only the safekeeping but also the privacy of vital data resources.
Enhancing Compliance
By controlling employee access to applications and data through stringent identity verification and ongoing validation, Zero Trust aids in regulatory compliance. SASE and Zero Trust models support organizations in fulfilling compliance standards by implementing rigorous access controls and overseeing user actions, which helps prevent risks related to data privacy breaches.
The protection of sensitive information is essential for maintaining stakeholder confidence, making regulatory compliance vital for organizations. The adoption of SASE and Zero Trust ensures that companies are equipped to handle the demands of contemporary regulation complexities with an all-encompassing security strategy that effectively manages enforcement of these rules.
Best Practices for Secure Access
Implementing best practices for secure access is crucial in safeguarding network resources and ensuring the integrity of sensitive data. Here are some key strategies to consider:
By combining these best practices, organizations can create a resilient security strategy that effectively protects network resources and sensitive data. Embracing both Zero Trust and SASE principles ensures a comprehensive approach to securing access, ultimately enhancing the overall security posture.
Challenges in Implementing SASE and Zero Trust
Organizations encounter considerable obstacles while adopting SASE and Zero Trust frameworks, despite their many advantages. One of the main hurdles is the complex integration involved since it requires significant modifications to existing security architectures and network infrastructures. There’s an acute requirement for professionals with the expertise necessary to manage and sustain zero-trust security models effectively.
For preserving a robust security posture in response to persistent threats within a changing network landscape, continuous monitoring is indispensable. It necessitates that organizations develop automated mechanisms that continuously detect threats and modify policies accordingly so that their trust security measures stay resilient against new challenges.
Integration Complexity
Incorporating SASE and Zero Trust into current infrastructure systems can be a complex task, necessitating significant modifications to the existing security setups. One of the primary challenges in merging these frameworks is overcoming skill shortages within teams, which can lead to issues during deployment and ongoing management. It’s essential to maintain continuous monitoring for detecting obstacles during integration while also adapting strategies as necessary to meet changing security needs.
It’s critical for organizations to meticulously strategize and implement the fusion of SASE and Zero Trust with their present systems, confirming compatibility with these sophisticated security approaches. By addressing both the complexities of integration and filling any expertise gaps, organizations are better positioned to successfully apply SASE and Zero Trust models, thereby enhancing their overall defense against threats.
Skill Gaps
A shortage of professionals adept in SASE and Zero Trust technologies can obstruct the proper adoption and maintenance of these systems. Organizations struggle to tap into the full potential of SASE and Zero Trust due to a lack of staff who are versed in contemporary security principles, presenting a significant hurdle for adopting such frameworks.
As more organizations recognize the need for expertise in SASE and Zero Trust trust principles, there is an increased demand for individuals proficient in these areas. To mitigate this challenge, it’s crucial that entities invest in training initiatives designed to elevate their IT workforce’s capabilities. This investment ensures that security teams possess the requisite skills to effectively administer and maintain sophisticated security infrastructures like those built on Sase and zero trust models.
Continuous Monitoring
Continuous vigilance through regular monitoring is key to maintaining security policies that can stand up against ever-changing cyber threats. This approach enables organizations to identify and react swiftly to potential security incidents, safeguarding their network’s integrity and the privacy of information contained within. Leveraging automated mechanisms for identifying threats and updating policies is indispensable in preserving a resilient defense amidst constantly shifting network landscapes.
By embracing ongoing surveillance methods, businesses ensure that their protective measures evolve alongside new risks and exposures, offering steadfast protection from digital intrusions. Such a vigilant strategy supports the effectiveness of SASE (Secure Access Service Edge) and Zero Trust frameworks crucially, enabling enterprises to secure their vital infrastructure as well as guard sensitive data against unauthorized access or breaches.
Summary
To sum up, merging SASE and Zero Trust creates a robust security solution well-suited for the intricate landscape of today’s network environments. This fusion boosts an organization’s defense capabilities, streamlines its approach to security, and leads to notable cost savings. The collaborative force of SASE and Zero Trust guarantees that only verified and authorized users can access essential assets, thus safeguarding the network’s integrity and confidentiality.
For successful deployment of SASE and Zero Trust frameworks, organizations must tackle potential hurdles like the complexity involved in integration efforts, skill shortages among personnel, and the imperative for ongoing vigilance. Surmounting these obstacles enables establishments to construct a sturdy yet adaptable defense architecture adept at thwarting contemporary cyber dangers. Adopt this advanced direction in network security by integrating both SASE and Zero Trust. Fortify your enterprise against nascent threats with assurance in its enduring adaptability.
Frequently Asked Questions
What is the primary difference between SASE and Zero Trust?
The primary difference between SASE and Zero Trust is that SASE integrates various network and security services, whereas Zero Trust emphasizes stringent access control and identity verification.
Understanding this distinction can help you choose the right approach for your security needs.
How does SASE enhance Zero Trust security?
SASE enhances Zero Trust security by consolidating multiple security services, which allows for comprehensive visibility, continuous verification, and effective management of user access, thereby strengthening overall security posture.
What are the key benefits of combining SASE and Zero Trust?
Combining SASE and Zero Trust enhances security posture, simplifies security strategy, and achieves cost efficiency. This integration creates a robust security model while streamlining management and reducing reliance on separate solutions.
What challenges might organizations face when implementing SASE and Zero Trust?
Organizations may encounter challenges such as integration complexity, skill gaps, and the necessity for continuous monitoring when implementing SASE and Zero Trust.
Careful planning and investment in training are essential to navigate these issues effectively.
How do SASE and Zero Trust frameworks help in securing remote workforces?
SASE and Zero Trust frameworks significantly enhance the security of remote workforces by verifying user identities and permissions, thus preventing unauthorized access. This approach ensures that only authenticated users can connect to network resources, significantly improving overall network integrity.


Comments ()