Top Strategies for Implementing Zero Trust Security Today

Zero Trust Security is a cybersecurity concept that means not trusting any entity by default, whether inside or outside your network. It requires every access attempt to be continuously verified. This article explores what Zero Trust Security is, why it’s essential, and the steps to implement it effectively in your organization. U.S. federal agencies are required to adhere to the NIST 800-207 standard for Zero Trust implementation, as mandated by an executive order from the Biden administration. The NIST 800-207 standard for Zero Trust is applicable to any organization, not just government entities.
Key Takeaways
- Zero Trust Security fundamentally shifts cybersecurity by requiring continuous verification of all access requests, eliminating default trust assumptions.
- Successful implementation of Zero Trust involves assessing current security posture, gaining executive buy-in, and prioritizing critical implementation tasks to enhance security measures.
- Key technologies, such as Identity and Access Management (IAM), Multi-Factor Authentication (MFA), and endpoint security, are essential for supporting Zero-Trust principles and effectively mitigating cyber threats. Effective cybersecurity measures are challenging due to the increasing number of devices and innovative attackers.
Understanding Zero Trust Security

The Zero Trust model marks a transformative shift in the methods organizations employ for cybersecurity. In contrast to conventional approaches which depend on defending the network perimeter, Zero Trust operates under the premise that potential threats may arise from within or beyond the network boundaries and thus demands constant validation of every request for access. By defaulting to distrust any entity, this method significantly strengthens an organization’s security stance. More than 80% of all attacks involve the use or misuse of credentials within the network, highlighting the importance of this approach.
We’re going to explore the fundamental tenets of Zero Trust and how it has progressed from classic security frameworks. Understanding these essential principles is vital when adopting zero trust policies that synchronize with your organization’s established cybersecurity procedures. The NIST cybersecurity framework guides organizations in identifying attacks, protecting systems, detecting threats, and recovering from attacks, making it a valuable resource for Zero Trust implementation.
Core Principles of Zero Trust
At the core of the zero trust model is a foundational principle that necessitates constant verification. This framework departs from traditional security methods, which operate on a ‘trust but verify’ basis, by insisting on persistent validation for access to resources in all scenarios—irrespective of where the user or their device is situated. The effect is robust authentication and authorization for every request to enter, along with encryption that significantly diminishes any chance of unauthorized entry. The NIST standard ensures compatibility and protection against modern attacks for a cloud-first model.
Integral to zero trust as well is embracing minimal privilege access. It stipulates providing users only with essential levels of access needed to perform their job functions effectively—reducing possible damage should internal threats arise.
Augmenting this protection strategy. Is network segmentation acting as an additional barrier by restricting accessibility exclusively within designated areas within the network environment. This impediment makes it notably more challenging for malicious entities attempting unauthorized movement across the network’s various segments.
Evolution from Traditional Security Models
The Zero Trust model represents a radical shift away from conventional security frameworks that traditionally emphasize boundary defenses. Previously, organizations tended to assume that threats mostly came from outside their networks, leading them to concentrate on fortifying the network’s outer edges. Nevertheless, the proliferation of cloud services and telecommuting has highlighted the weaknesses in this method.
It is anticipated that by and in 2025, many companies will have embraced Zero-Trust solutions to tackle internal and external vulnerabilities. This transition highlights how crucial it is for every user and device to be authenticated regardless of their physical location to achieve thorough protection.
Employing zero-trust principles offers an enhanced security framework that is more robust and flexible than previous models. It is better equipped to combat contemporary cyber threats.
Implementing Zero Trust in Your Organization

Implementing a zero-trust security framework begins with examining your existing security stance. This involves scrutinizing the users, devices, and applications that have access to your network to pinpoint potential weak spots. Gaining insights into these areas will help you set priorities for the steps needed during implementation while aiming to reduce interruptions.
Critical actions include tasks such as evaluating your current security position, securing support from top management, and arranging the order of tasks necessary for deployment. These tactics are designed to ease you through the intricacies of moving towards a zero-trust model, ensuring a more fluid introduction of this approach.
Assessing Current Security Posture
Traditional security frameworks are proving insufficient as cloud services and remote work become more prevalent, signaling the necessity for a stronger strategy. To gauge your existing security posture, it’s essential to pinpoint specific protect surfaces—vital assets requiring safeguarding—and assess the associated risk levels. By doing this, organizations can prioritize applying Zero Trust principles strategically to fortify these most crucial elements first.
By segmenting the adoption of Zero Trust into smaller, manageable stages, organizations can concentrate on areas that will have significant impact while progressively broadening their Zero Trust practices. Determining which tasks take precedence based on the criticality of assets and corresponding risks leads to smarter allocation of resources and bolsters your overall security framework.
Gaining Leadership Buy-In
Attaining the backing of top executives is essential for successfully embarking on a Zero-Trust strategy. An influential persuasion tactic is to convince them of the prospects of a return on investment through diminishing risks. Emphasizing concrete outcomes, such as fewer data breach occurrences and heightened adherence to cybersecurity best practices, can bolster your argument.
Presenting well-defined business scenarios along with the anticipated ROI from improving security protocols can help gain executive endorsement. Pointing out that implementing these measures step-by-step will help assuage fears regarding operational disruptions, thereby facilitating easier procurement of the required resources.
Prioritizing Implementation Tasks
Conducting a detailed evaluation of your organization’s current security weaknesses is essential for pinpointing the most vital regions to apply Zero Trust principles. Critical focal points should encompass managing user identities, safeguarding data, and securing endpoints. By charting the present safeguards and pinpointing deficiencies, you can establish what areas require immediate attention in your Zero Trust agenda.
Organize initiatives by considering the degree of risk they mitigate, with emphasis on domains that could yield considerable enhancements in security when addressed first. The phased application of Zero Trust measures enables ongoing refinement and verification throughout each phase, which facilitates a more seamless adoption process while enhancing overall defense mechanisms.
Cybersecurity Best Practices for Zero Trust Implementation
Implementing a Zero Trust model requires a comprehensive approach to cybersecurity. Here are some best practices to consider:
- Conduct Regular Cybersecurity Assessments: Regular assessments are crucial for identifying vulnerabilities and weaknesses in your system. By conducting thorough cybersecurity assessments, organizations can proactively address potential threats before they can be exploited. This continuous evaluation helps in maintaining a robust security framework that adapts to evolving cyber threats.
- Implement a Robust Security Framework: A well-structured security framework provides a systematic approach to managing cybersecurity risks. It ensures that all aspects of cybersecurity are addressed, from user identity management to access control and data protection. A comprehensive security framework is the backbone of a successful Zero Trust implementation.
- Use Threat Intelligence: Staying ahead of emerging threats and vulnerabilities is essential for effective cybersecurity. By leveraging threat intelligence, organizations can gain insights into potential risks and take proactive measures to protect their systems. Threat intelligence helps in identifying and mitigating threats before they can cause significant damage.
- Implement Conditional Access: Conditional access ensures that access to sensitive data is granted only to authorized users and devices. By setting specific conditions for access requests, organizations can reduce the risk of unauthorized access and protect sensitive information. This approach aligns with the Zero Trust model’s principle of continuous verification.
- Monitor User Identity and Access Requests: Continuous monitoring of user identity and access requests is vital for detecting and preventing unauthorized access attempts. By keeping a close watch on who is accessing what, organizations can quickly identify suspicious activities and take appropriate actions to mitigate risks.
- Ensure Data Backups: Data backups are essential for disaster recovery in cybersecurity. Regularly backing up data ensures that organizations can recover quickly and minimize disruptions in the event of a cyber attack.
Secure Your Remote Workforce
With the rise of remote work, securing your workforce is crucial to preventing cyber threats. Here are some best practices to consider:
- Implement Multi-Factor Authentication (MFA): Multi-factor authentication adds an extra layer of security to the login process, making it more difficult for attackers to gain access. By requiring multiple forms of verification, MFA ensures that even if one credential is compromised, unauthorized access is still prevented.
- Enable Zero Trust Network Access (ZTNA): Instead of relying on traditional VPNs, organizations should adopt Zero Trust Network Access (ZTNA) to connect remote users securely to private applications. ZTNA enforces least-privilege access based on user identity, device posture, and real-time risk assessment. Solutions like secure access service edge (SASE) platforms integrate security and networking to provide seamless, policy-driven access without exposing applications to the open internet.
- Implement Endpoint Security: Endpoint security ensures that remote devices, such as laptops and smartphones, are secure and up-to-date. By deploying endpoint security solutions, organizations can protect remote devices from malware, ransomware, and other cyber threats, reducing the risk of data breaches.
- Use Microsegmentation for Access Control: Microsegmentation restricts access to applications and data based on identity and context, reducing the attack surface. By segmenting access at a granular level, organizations can prevent lateral movement in case of a security breach and enforce strict access controls for remote users.
- Conduct Regular Security Awareness Training: Regular security awareness training helps remote employees understand the importance of cybersecurity and how to identify and report suspicious activity. By educating employees about common cyber threats and best practices, organizations can create a security-conscious remote workforce.
People, Processes, and Technology
A successful Zero Trust implementation requires a combination of people, processes, and technology. Here are some best practices to consider:
- Develop a Comprehensive Security Policy: A comprehensive security policy outlines the organization’s approach to cybersecurity and ensures that all employees understand their roles and responsibilities. This policy should cover all aspects of security, from data protection to incident response, and provide clear guidelines for employees to follow.
- Implement Incident Response Planning: Incident response planning ensures that the organization is prepared to respond quickly and effectively in the event of a cyber attack. By having a well-defined incident response plan, organizations can minimize the impact of security incidents and recover more swiftly.
- Use Technology to Automate Security Processes: Technology can help automate security processes, reducing the risk of human error and improving efficiency. Automation tools can streamline tasks such as monitoring, threat detection, and response, allowing security teams to focus on more strategic activities.
- Provide Ongoing Security Training and Awareness: Ongoing security training and awareness help employees understand the importance of cybersecurity and how to identify and report suspicious activity. Regular training sessions and awareness programs ensure that employees stay informed about the latest security threats and best practices.
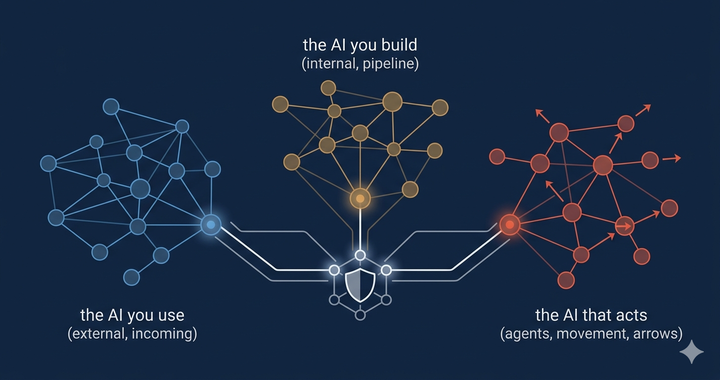
Key Technologies Supporting Zero Trust

Organizations must constantly innovate their security strategies to combat the swift progression of cyber threats. It is crucial for these entities to regularly refine their Zero Trust approaches and incorporate cutting-edge technologies in order to address new vulnerabilities effectively. We will delve into essential technologies that bolster Zero Trust, encompassing Identity and Access Management (IAM), Multi-Factor Authentication (MFA), and endpoint security within this section.
Employing such technologies proves fundamental when instituting zero trust policies, as they provide robust protection across the board. These tools play a pivotal role in strengthening an organization’s cybersecurity defenses, ensuring its resources are secure against the dynamic nature of cyber threats.
Identity and Access Management (IAM)
Technologies for Identity and Access Management (IAM) are essential in overseeing both user identities and the permissions they have within various systems. By implementing access control based on roles through IAM, it is possible to confine users’ access according to their professional duties, thereby guaranteeing that only those who are authorized can access sensitive data.
By employing Single Sign-On (SSO), not only is the authentication process made more straightforward—enhancing the overall experience for users—but security is also upheld. Incorporating context-aware access controls, which form an integral part of a Zero Trust approach, ensures an even stronger defense against illegitimate attempts at accessing sensitive information.
Multi-Factor Authentication (MFA)
Multi-Factor Authentication (MFA) enhances security by requiring users to provide two or more verification methods when logging in. This significantly reduces the likelihood of unauthorized access, even if a password is compromised. In fact, implementing MFA can reduce the risk of unauthorized access by 99%.
MFA, a key aspect of Zero Trust, adds a layer of security for remote access, ensuring thorough authentication of each request. Multiple forms of verification help organizations better protect accounts and data from cyber threats.
Endpoint Security
Protective strategies for devices like computers, smartphones, and tablets are essential in safeguarding against cyber threats since these devices can become gateways to network vulnerabilities. Ensuring the security of these endpoints is crucial as effective solutions must be able to detect and counteract threats instantaneously to reduce potential harm.
By overseeing and controlling access through gadgets such as laptops and smartphones, unauthorized entry and compromises of data can be averted. As an integral component of Zero Trust frameworks, endpoint security guarantees that all points of access remain secure under vigilant observation.
Threats and Risks in Zero Trust Implementation
Implementing a Zero Trust model is not without risks. Here are some threats and risks to consider:
- Phishing and Social Engineering: Phishing and social engineering attacks can trick employees into revealing sensitive information or gaining unauthorized access. These attacks often exploit human vulnerabilities, making it essential to educate employees about recognizing and avoiding such threats.
- Identity Theft: Identity theft can allow attackers to gain access to sensitive data and systems. By stealing user credentials, cybercriminals can impersonate legitimate users and bypass security measures. Implementing strong identity verification processes is crucial to prevent identity theft.
- Cyber Attacks: Cyber attacks can compromise sensitive data and disrupt business operations. From ransomware to distributed denial-of-service (DDoS) attacks, cyber threats are constantly evolving. Organizations must stay vigilant and adopt advanced security measures to defend against these attacks.
- Insider Threats: Insider threats can come from employees or contractors who have authorized access to sensitive data and systems. These threats can be intentional or accidental, making it important to monitor user activities and implement strict access controls to mitigate risks.
By understanding and addressing these threats and risks, organizations can enhance their Zero Trust implementation and ensure a more secure environment.
Zero Trust Use Cases

The principles of Zero Trust Security are versatile, offering strong protection tailored to a variety of organizational requirements. This segment will delve into the practical applications of Zero Trust, focusing on securing remote employees, defending against exposure to sensitive data and reducing the risks posed by insider threats.
Looking at these particular examples provides insight into how Zero Trust tackles distinct challenges within cybersecurity and bolsters an organization’s defense mechanisms.
Protecting Remote Employees
By consistently authenticating user identities throughout access sessions, Zero Trust Security improves the safety of remote work. It confirms that each request for access is authenticated and authorized, independent of the user’s physical location.
Integrations such as Cisco Secure Remote Worker can enhance protection for those working remotely by embedding Zero Trust concepts within current systems. This ongoing validation process allows organizations to fortify their defenses against cyber threats aimed at remote employees more effectively.
Safeguarding Sensitive Data
By adopting a zero trust model, organizations can diminish the risks related to data breaches through the elimination of inherent trust and validating every single connection. The enhancement of data protection is achieved by requiring authentication and authorization for each request for access.
Sensitive information is protected using IAM (Identity and Access Management) systems that oversee user identities and their permissions, substantially reducing the chances of unauthorized access to sensitive resources and thereby minimizing potential data breaches.
Mitigating Insider Threats
By continuously monitoring user activities and evaluating trust levels in a context-sensitive manner, Zero Trust principles are able to detect insider threats. This proactive strategy promptly recognizes and mitigates atypical actions that suggest the presence of insider threats.
With behavior analytics as an integral part of Zero Trust, organizations can effectively pinpoint and tackle potential insider threats. The practice of constant verification coupled with ongoing surveillance forms a strong protective barrier against the changing landscape of cyber threats.
Overcoming Challenges in Zero Trust Implementation
The process of implementing Zero Trust Security may face obstacles such as pushback from organizational culture and the difficulty of aligning it with outdated systems. To overcome these issues, strong strategies for managing change are essential, along with a comprehensive grasp of what might hinder its acceptance.
In delving into typical hurdles encountered during Zero Trust implementation, we aim to offer methods to overcome them. These include finding an equilibrium between security and user convenience, ensuring compatibility with current systems, and addressing the intricacies associated with compliance and regulatory demands.
Balancing Security and Usability
Adopting user-friendly security protocols minimizes friction while ensuring robust protection in Zero Trust environments. Strong access controls prevent unauthorized viewing of critical data while maintaining a seamless user experience.
The Zero Trust approach reduces the attack surface by limiting access points and enforcing least privilege access. Preventing lateral movement within networks significantly minimizes the impact of successful attacks.
Integrating with Existing Systems
Older systems frequently do not possess the flexible features necessary to accommodate the contemporary Zero Trust framework, which can lead to considerable difficulties in integration. When attempting to incorporate Zero Trust technologies into these legacy systems, compatibility problems may surface, making it essential for updates to be made for them to function correctly.
When blending Zero Trust strategies with antiquated systems, it might be more practical to make incremental adjustments instead of full-scale replacements. Meticulous planning and thorough testing are crucial for a smooth shift that effectively tackles any issues related to compatibility.
Compliance and Regulatory Considerations
Ensuring alignment of Zero Trust implementations with industry-specific compliance requirements is a critical aspect of navigating the regulatory landscape. Organizations need to make certain that their strategies for Zero Trust are in compliance with legal standards, which is vital for maintaining adherence to these regulations.
When implementing Zero Trust, organizations have to conduct thorough cybersecurity assessments to gauge and align their current security stance with necessary regulatory standards. This involves an extensive review of existing controls as well as identifying any potential shortcomings in order to fulfill the compliance obligations effectively.
Benefits of Zero Trust Security

Implementing a Zero Trust framework provides several significant gains, such as improved identification and management of threats, diminished risk levels, and augmented adaptability. These benefits assist organizations in fulfilling intricate compliance mandates while elevating their general trust security stance.
We’ll delve into the primary advantages that Zero Trust Security offers, including advanced detection and reaction to threats, decreased risk with lessened consequences on operations, along with enhanced versatility and expansion capacity. Recognizing these perks is crucial for securing leadership backing and ensuring that Zero Trust strategies are synchronized with wider business objectives.
Enhanced Threat Detection and Response
By constantly monitoring context and behavior, Zero Trust Security improves the identification of threats, allowing for faster reactions to potential risks. The integration of advanced technologies such as AI and machine learning elevates Zero Trust’s capabilities by streamlining the automation of threat detection and reaction processes.
The use of AI-driven analytics assists in recognizing unusual activity, offering valuable information that strengthens access controls within a Zero Trust framework. Through this proactive strategy, organizations are equipped to quickly and efficiently detect and counteract complex cyber attacks.
Reduced Risk and Minimized Impact
By adopting multi-factor authentication (MFA), the likelihood of unwarranted access to sensitive data is considerably decreased. Establishing explicit access controls plays a vital role in alleviating security risks, confirming that only approved individuals can enter crucial systems.
The implementation of persistent monitoring alongside immediate response measures helps curtail damage at the moment incidents take place, thereby reducing their aggregate effect. Dividing a network into segments aids in confining breaches and hinders attackers from moving laterally within the network.
Increased Flexibility and Scalability
Security frameworks based on Zero Trust are flexible, enabling organizations to adjust their security protocols in response to emerging threats and changing operational requirements. They suit businesses of all sizes and can be applied within diverse technological settings.
Models rooted in the principles of Zero Trust evolve alongside contemporary workforces, providing secure backing for remote operations and fluid business circumstances. By implementing tools such as single sign-on and multi-factor authentication, organizations can reduce inconvenience for users while simultaneously boosting overall security measures.
Future Trends in Zero Trust Security
Technological progress, including artificial intelligence (AI) and machine learning, is essential to the ongoing development of Zero Trust Security. These cutting-edge technologies are significantly enhancing the capacity for advanced threat intelligence within this security model.
In our examination of upcoming tendencies in Zero Trust Security, we will consider how AI and machine learning integration will advance beyond just IT sectors while fostering constant innovation. Such trends are poised to define the trajectory of cybersecurity and equip organizations with the tools necessary to preventively address evolving threats.
Integration with AI and Machine Learning
By incorporating AI and Machine Learning, Zero Trust security is bolstered through constant vigilance and instantaneous identification of potential threats. These advancements streamline the process of assessing risk by automating it, which enhances the effectiveness of security measures within a Zero Trust framework.
Leveraging AI for analytics aids in spotting unusual activity patterns, which fortifies access controls rooted in the principles of Zero Trust. This proactive approach to detecting weaknesses enables organizations to address possible threats before they can evolve into actual risks.
Expanding Beyond IT
Organizations are realizing the importance of implementing Zero Trust principles within operational technology (OT) settings to ensure security for both information technology systems and vital infrastructure components. The adoption of these principles in OT domains marks an extension from their conventional application within IT frameworks.
The scope of Zero Trust is expanding to cover operational technology, which involves industrial control systems as well as Internet of Things (IoT) devices. By doing so, it offers thorough protection that spans every aspect involved in an organization’s functioning processes.
Continuous Innovation and Adaptation
Continuous advancements in Zero Trust Security enable organizations to adapt to emerging attack vectors and tactics. By consistently assessing security protocols, they can maintain their effectiveness against continuously changing threats.
Incorporating agile methodologies allows for faster reaction times to new cybersecurity challenges. Through consistent training and awareness initiatives, organizational teams stay informed about the most recent developments in security practices and innovations, thus preserving a strong stance on trust security.
Summary
In summary, the Zero Trust Security model provides a robust and flexible strategy to address contemporary cybersecurity issues. Through constant validation of every request for access and adherence to the least privilege principle, organizations can markedly improve their defensive measures and safeguard against emerging threats.
The adoption of Zero Trust fundamentals necessitates meticulous preparation, endorsement from top management, and an incremental rollout strategy. Nevertheless, the advantages—such as improved identification of threats, diminished risk levels, enhanced adaptability, and better scalability—justifies its implementation for any organization aiming to strengthen its security in today’s digital environment. Embrace Zero Trust Security to ensure your organization’s long-term protection. In today's connected world, everyone benefits from advanced cyberdefense programs.
Frequently Asked Questions
What is Zero Trust Security?
The Zero Trust Security model is a framework in cybersecurity that requires unrelenting confirmation for every request to access resources, based on the belief that trust should never be assumed automatically for any entity, whether it comes from inside or outside the network.
By adopting this strategy, safety measures are significantly strengthened by making security an incessant concern without considering where the user is situated.
How does Zero Trust differ from traditional security models?
The concept of zero trust stands in stark contrast to conventional security models by discarding the idea that there exists a safe boundary. It operates on the principle that potential threats may arise not just from outside, but also from within, necessitating continuous authentication and confirmation for every attempt at access.
This change underscores a vigilant stance towards security, guaranteeing that trust is always earned and never presumed.
What are the core principles of Zero Trust?
The core principles of Zero Trust are continuous verification, the principle of least privilege, and network segmentation, which collectively mandate that all access requests must be authenticated, authorized, and encrypted.
Adhering to these principles enhances security by minimizing trust assumptions.
What are some common challenges in implementing Zero Trust?
Due to cultural pushback, challenges in assimilating with outdated systems, and issues related to adherence to regulations, the implementation of Zero Trust can present difficulties.
To surmount these obstacles successfully requires meticulous strategizing and proficient management of change.
What are the benefits of adopting Zero Trust Security?
Adopting Zero Trust Security significantly enhances threat detection and response while reducing risk and minimizing impact. This approach also increases flexibility, scalability, and aids in meeting complex compliance requirements, thereby improving overall security posture.


Comments ()