Understanding Secure Service: How to Protect Your Data in the Cloud

Want to keep your cloud data safe? Secure service solutions protect your sensitive information from cyber threats. Learn what secure service is, why you need it, and how to use it effectively. Verifying user identity is crucial in these solutions to ensure only authorized access to applications and data.
Key Takeaways
- Cybersecurity services are essential in protecting sensitive data from breaches, with Security Service Edge (SSE) solutions providing comprehensive protection for cloud services.
- Zero Trust Security emphasizes strict access controls and continuous verification, enhancing protection through strategies like microsegmentation and integration with SSE solutions.
- Unified solutions simplify data security management, improve operational efficiency, and enable effective continuous monitoring, making them suitable for organizations in a remote work environment.
- Verifying user identity is crucial in enhancing Zero Trust security, ensuring only authorized access to applications and data, and safeguarding against potential threats in a cloud-centric environment.
The Importance of Secure Service in Today's Digital Landscape

In today’s digital age, where cyber threats are escalating, the role of cyber security services is more critical than ever. These services play an essential part in protecting sensitive information from being compromised and misused by unauthorized individuals for both private users and corporations. The adoption of formidable cyber security strategies extends beyond data protection—it serves as a preventive barrier against potential financial losses and harm to reputation that could have enduring repercussions on any organization.
Security Service Edge (SSE) solutions stand at the forefront of combating these cyber challenges. SSE merges various security tools into one cohesive system offering comprehensive defense mechanisms for computers and networks alike. Those who employ SSE solutions notice marked advancements in protecting public cloud-based operations and adherence to stringent access protocols—underscoring their efficacy within our digitally-driven society. Verifying user identity plays a crucial role in protecting sensitive information and ensuring only authorized access to applications and data.
As digital threats evolve with increasing complexity, conventional methods fall short when it comes to adequately shielding organizations from advanced types of attacks. That’s why modernized security service offerings deliver layered approaches towards safeguarding data. They enable businesses not just reactively respond, but proactively counteract emerging dangers – securing organizational stability through continuous vigilance over precious assets like proprietary data while maintaining uninterrupted daily functions.
What is Security Service Edge (SSE)?
Security Service Edge (SSE) is a cloud-native security solution designed to provide secure access to corporate resources, applications, and data, particularly for remote workers and users. As a crucial component of a comprehensive Secure Access Service Edge (SASE) strategy, SSE focuses on security enforcement and data protection.
SSE solutions offer a range of security capabilities that include access control, threat protection, data security, security monitoring, and acceptable use control functionality. By integrating these capabilities, SSE ensures that users can securely access necessary services while protecting sensitive data from potential cyber threats. This holistic approach to security is essential in today’s digital landscape, where remote work and cloud-based operations are increasingly prevalent.
Zero Trust Security: A Modern Approach
Zero Trust Security represents a paradigm shift in protecting sensitive data, founded on the principle that no person or system, whether inside or outside of an organization’s networks, is assumed to be secure without proper validation. By focusing on rigorous access restrictions and persistent verification for both users and devices, this model overhauls conventional trust security methods. Verifying user identity alongside device security is crucial in the Zero Trust model to ensure only authorized access to applications and data, safeguarding against potential threats in a cloud-centric environment.
Central to the Zero Trust framework is microsegmentation. It effectively reduces potential avenues for attacks by partitioning networks into separate zones. If an attacker breaches one area of the network under this strategy, their impact remains localized due to containment measures preventing lateral movement throughout other segments. Crucially, analytics bolster Zero Trust practices by providing insights regarding user behavior patterns and helping identify risks associated with granting access permissions.
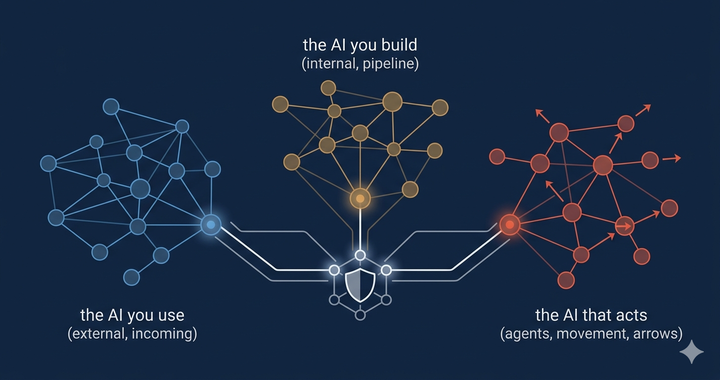
As threats continue to evolve in complexity and sophistication, organizations embracing a Zero Trust approach must perpetually reassess their defenses against such dangers. Reports from companies employing Secure Service Edge (SSE) indicate strengthened security through implementing Zero Trust Network Access (ZTNA), which ensures safe connections directly between users and applications circumventing reliance upon traditional network structures. As more workers operate remotely today than ever before, adopting such cutting-edge protective strategies has become indispensable for shielding critical information assets in our increasingly digital world.
Core Capabilities of a Secure Service Edge
A robust Secure Service Edge (SSE) solution encompasses several core capabilities to ensure comprehensive security for remote workers and users. These capabilities include:
- Access Control: SSE solutions must effectively manage and control user access to corporate resources, applications, and data. This ensures that only authorized users can access sensitive information, thereby reducing the risk of unauthorized access.
- Threat Protection: Detecting and preventing threats such as malware, phishing, and other cyber attacks is a critical function of SSE solutions. By providing real-time threat protection, SSE helps safeguard corporate resources from potential breaches.
- Data Security: Protecting sensitive data is paramount. SSE solutions employ encryption, data loss prevention (DLP), and data security posture management to ensure that sensitive information remains secure, whether in transit or at rest.
- Security Monitoring: Continuous monitoring of user behavior and network activity is essential for identifying and responding to security threats. SSE solutions provide real-time visibility into security incidents, enabling swift action to mitigate risks.
- Acceptable Use Control: Enforcing acceptable use policies ensures that users access corporate resources and applications in a secure and compliant manner. This capability helps maintain organizational security standards and regulatory compliance.
By integrating these core capabilities, SSE solutions provide a comprehensive security framework that protects sensitive data and corporate resources from evolving cyber threats.
Secure Web Gateway (SWG)
A Secure Web Gateway (SWG) is a vital component of a Secure Service Edge (SSE) solution. SWGs provide secure internet access for remote workers and users, protecting against web-based threats and enforcing acceptable use policies.
SWGs offer real-time threat protection, data loss prevention, and security monitoring, ensuring that users access the internet securely and compliantly. By filtering and inspecting web traffic, SWGs prevent malicious content from reaching users and protect sensitive data from being exfiltrated. This comprehensive approach to web security is essential for maintaining a secure and productive remote work environment.
Incorporating SWGs into an SSE solution enhances overall security by providing an additional layer of protection against internet-based threats, ensuring that users can safely access the web without compromising corporate security.
Simplifying Data Security with Unified Solutions
Unified SSE solutions are crafted to consolidate the management of data security by amalgamating diverse tools and diminishing operational intricacies. These solutions ease workflows and mitigate the complexities tied to handling an array of cybersecurity utilities, positioning them as very beneficial for large-scale enterprises. A key component of these unified solutions is user identity verification, which, alongside device security and context, ensures only authorized access to applications and data. The integration features facilitate a harmonious operation among different security instruments, boosting productivity while curtailing potential risks in operations.
In supporting scalable remote work strategies, cloud-based infrastructures are crucial due to their inherent ability to adjust seamlessly with fluctuating needs without any limitations related to physical hardware. SSE solutions provide instantaneous oversight and governance across distant endpoints, maintaining robust security without impeding network throughput.
Such an amalgamation of functionalities positions unified SSE solutions as exemplary options for entities aspiring to amplify their data protection measures across varied settings.
AI-Driven Security Enforcement
Leveraging AI-driven security enforcement elevates data protection through the use of sophisticated technologies designed to identify and counteract threats instantaneously. AI-driven technologies can also enhance user identity verification, ensuring that only authorized access to applications and data is permitted. The deployment of an AI-enabled, multi-tiered defense system delivers exhaustive safeguards against a spectrum of cyber threats. Features that enable automatic detection expedite the recognition and reaction processes to potential security infractions, thereby bolstering the overall defensive stance of an entity.
The synergy between AI-facilitated threat discovery and mechanized response protocols ensures rapid action by security teams in mitigating risks, curtailing chances for data breaches or similar cyber incursions. Infusing artificial intelligence into the realm of security measures significantly augments a firm’s capacity to safeguard sensitive information and uphold a formidable structure for securing its digital assets.
Data-Centric Technologies for Enhanced Protection
Technologies focused on data within SSE solutions provide constant supervision and protection for sensitive information. These technologies equip organizations with the ability to conduct stringent, ongoing monitoring that defends their sensitive data against breaches. The adoption of SSE has empowered organizations to more effectively manage their sensitive information through Cloud Data Loss Prevention (DLP) mechanisms, which secure data whether it is being transferred or stored. Additionally, verifying user identity plays a crucial role in protecting sensitive data by ensuring that only authorized users can access applications and information.
By marrying perpetual oversight with potent control strategies, an organization’s capacity to shield its data from threats is significantly bolstered. Centering security efforts directly on the safety of the data itself rather than relying solely on external barriers ensures that an organization’s most critical assets are defended from potential risks.
Real-World Applications and Benefits

In an effort to mitigate the risks of data breaches, businesses across a multitude of industries have embraced secure service strategies. Financial entities, healthcare institutions, and retail chains are among those who have integrated SSE solutions for safeguarding critical customer information while adhering to regulatory mandates. These implementations yield concrete advantages by diminishing instances of data compromise, bolstering consumer confidence, and elevating efficiencies within their operations.
The impact made by adopting secure service strategies is underscored by organizational simplification in security processes and a fortified overall stance on protection measures. Such approaches empower enterprises in defending their proprietary resources against threats while harmonizing security protocols and fostering safer conditions for both clientele and staff members.
Demonstrated through practical applications within real-life contexts, it’s clear that secure service methodologies play a pivotal role in reducing vulnerabilities associated with handling sensitive information as well as amplifying the robustness of data security frameworks at large. Additionally, verifying user identity is crucial in these implementations, ensuring that only authorized individuals gain access to applications and data, thereby enhancing Zero Trust security.
Scalability and Flexibility for Remote Work

With the growing prevalence of remote work, it is critical for organizations to implement security solutions that are both scalable and adaptable in order to safeguard their online activities. This has become increasingly important given the heightened risk of cyber threats. As a result, employing Zero Trust as a central strategy has gained significance in protecting sensitive data within widely distributed networks.
To improve user experience amid an expanding workforce, scalable IT support is vital. It ensures uniform performance and swift resolution of problems. Organizations adopting secure service edge (SSE) solutions have experienced improved security when remotely accessing resources and better traffic control. Verifying user identity is crucial in these environments to ensure that only authorized individuals can access applications and data, thereby enhancing overall security.
Such SSE solutions enable companies to smoothly scale their resource allocation, cater to an increasing number of devices and users, and effectively handle surges in demand that may occur seasonally.
Integrating SD-WAN for Enhanced Connectivity
Incorporating SD-WAN significantly improves connectivity, acting as a transformative element for network performance. The technology operates by leveraging diverse transport methods in tandem and making decisions on the best path in real-time, considering present network statuses. This results in secure connections to cloud services that are both direct and fast, enhancing application efficiency while minimizing delays that would typically occur when routing through data centers.
By adopting SD-WAN, managing your network becomes streamlined due to its centralized control capabilities. Businesses have the advantage of being able to configure and solve issues within their networks from one unified interface. Such a setup supports effortless expansion of the business’s networking infrastructure without having to deal with intricate modifications of pre-existing systems—enabling growth scalability while also cutting down expenses by substituting costly MPLS links with more cost-effective broadband options. Additionally, secure SD-WAN implementations benefit from verifying user identity, ensuring that only authorized users gain access to applications and data, thereby enhancing overall security.
Lastly, SD-WAN is designed to bolster network reliability and ensure uninterrupted operation for enterprises by providing features such as automatic re-routing of traffic along with instant failover solutions during disruptions or downtimes.
Key Features to Look For in a Secure Service Solution

In the process of choosing a secure service solution, it is imperative to focus on several fundamental attributes. In environments adhering to Zero Trust principles, incorporating Multi-factor authentication (MFA), which demands various types of identity confirmation for access, is vital. It’s essential to have financial backing based on prioritized security requirements in place before engaging with potential vendors.
Additionally, verifying user identity is a critical feature in secure service solutions, ensuring that only authorized users gain access to applications and data. It’s important to conduct thorough research and analysis when comparing prospective vendors by assessing their ability to scale, how well they integrate with current tools you use, and any consequences relating to compliance. When you narrow down your choices, directly interrogate these preferred vendors with comprehensive inquiries that guarantee their services align precisely with the unique security needs of your organization.
Ensuring there is a match between what the vendor offers in terms of capabilities and your own organizational security demands plays a crucial role in effectively protecting data.
How to Deploy and Manage Secure Service Solutions
Implementing secure service solutions within an organization requires a methodical strategy. It is essential to introduce new security measures gradually and conduct tests in a controlled setting before rolling them out across the entire organization. During deployment, verifying user identity is crucial to ensure that only authorized access to applications and data is granted, thereby enhancing overall security. This careful approach guarantees that sensitive data remains protected during each step of implementation.
To preserve the integrity of these deployed service solutions, it is important for organizations to consistently manage and refine their security strategies. By constantly monitoring and improving these services, organizations can respond effectively to changing threats and uphold strong protection for their sensitive data.
Monitoring and Reporting for Continuous Improvement
Enhanced network visibility and continuous monitoring are essential for bolstering security protocols. By keeping a watchful eye on user behavior, organizations can swiftly identify any odd or suspicious activity. Robust monitoring solutions should seamlessly merge with current security systems, enabling the real-time analysis of data and immediate notifications of potential threats. Additionally, verifying user identity plays a crucial role in monitoring and reporting, ensuring that only authorized users access sensitive applications and data.
Having a unified platform for logging and reporting sharpens an organization’s capacity to steer their security strategies using empirical evidence. It is beneficial to carry out subsequent evaluations between six months to one year after putting new security measures into action. This practice assists in determining the success of those interventions and allows for the cyclical refinement of policies informed by insights drawn from ongoing monitoring efforts.
Summary
To safeguard data within the cloud, a comprehensive strategy that integrates cutting-edge security measures, adheres to Zero Trust security principles, utilizes AI for enforcement, and focuses on data-specific technologies is crucial. Verifying user identity alongside device security and context ensures only authorized access to applications and data, ultimately safeguarding against potential threats in a cloud-centric environment. Organizations can shield sensitive information from unauthorized access by implementing secure service solutions while simultaneously streamlining their operations and strengthening their overall trust security framework.
In our journey through the digital realm, it’s essential to emphasize the significance of robust trust security practices. Through ongoing vigilance and enhancement of these security solutions, organizations are better equipped to confront emerging cyber threats head-on—maintaining the safety of their sensitive data. The investment in securing services reflects not merely an operational requirement but also a dedicated pledge towards preserving a secure digital landscape into the future.
Frequently Asked Questions
What is Zero Trust security?
Zero. Zero. Trust security emphasizes that no entity, whether inside or outside the network, is inherently trustworthy, mandating stringent access controls and ongoing identity verification to enhance network security.
This approach significantly reduces the risk of unauthorized access and data breaches.
How do AI-driven security enforcement solutions work?
AI-driven security enforcement solutions enhance protection by utilizing advanced technologies for real-time threat detection and automated response, creating a multi-layered defense system.
This proactive approach ensures more effective safeguarding against potential security breaches.
What are the benefits of integrating SD-WAN for connectivity?
Integrating SD-WAN significantly enhances application performance and scalability while simplifying network management and reducing costs by replacing costly MPLS connections.
This ensures a more efficient and effective connectivity solution for your organization.
How can organizations ensure effective deployment of secure service solutions?
To ensure effective deployment of secure service solutions, organizations should implement security solutions gradually, test them in controlled environments, and continuously manage and optimize their performance.
This strategy helps maintain a strong security posture and reduces potential vulnerabilities.
Why is continuous monitoring important for cybersecurity?
Consistent surveillance is essential for cybersecurity because it allows organizations to quickly identify questionable activities and make educated decisions about security using analysis of up-to-the-minute data.
By adopting this vigilant strategy, the improvement in incident response speed and enhancement of the general defensive stance against threats are greatly increased.


Comments ()